Platform
No-code workflow builder

Designed for every department
Discover workflow automation made simple
Ease your workload with automated AI workflows
Platform

Discover workflow automation made simple
Ease your workload with automated AI workflows
Solutions
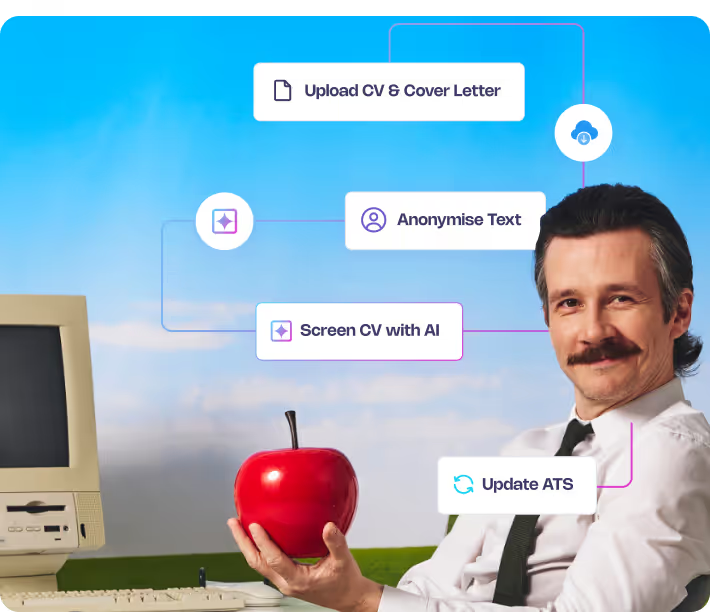
Automate any process with AI
Explore some of our most popular use cases
By Industry

Retail

Hospitality & tourism

Healthcare & pharmaceuticals

Government & public admin

Aviation

View All
HR automation that works for you
Solutions
Explore some of our most popular use cases
About 50skills
Powerful automation, simple to use

Helping you automate without the hassle
Passionate about making AI automation effortless
About 50skills
Passionate about making AI automation effortless
Resources
Got a question? We have answers

Discover smarter ways to work
Find insights, tools, and examples to optimise your workflows
Start your Journey, get the knowledge
Resources

Start your Journey, get the knowledge
Workflow-Wednesdays: Sign up for a weekly session column about building automated journeys
30
Sign up today50skills triumphs as category winner and secures 2nd Place overall at HR Technologies UK!
7
Learn more



.webp)


.webp)